Видео с ютуба Risk-Based Access Control

Risk-Based Authentication Explained

Role-based access control (RBAC) vs. Attribute-based access control (ABAC)

Risk based Access Control

Beyond Identity + CrowdStrike: The Deepest IAM Integration for Continuous, Risk-Based Access

How to Deploy Risk-Based Policies with Microsoft Entra ID

Entra ID P1 vs P2: The Magic of Risk-Based Conditional Access

SUNRISE - Risk-Based Access Control (RiBAC) training video

Live Demo of Risk-Based Access Control through Juniper & WootCloud HyperContext

How to implement a Risk Based Approach in your Compliance Programme

Mastering the Risk-Based Approach in Compliance

Объясните модели контроля доступа | Дискреционный DAC, обязательный MAC, RBAC, правила, атрибуты,...
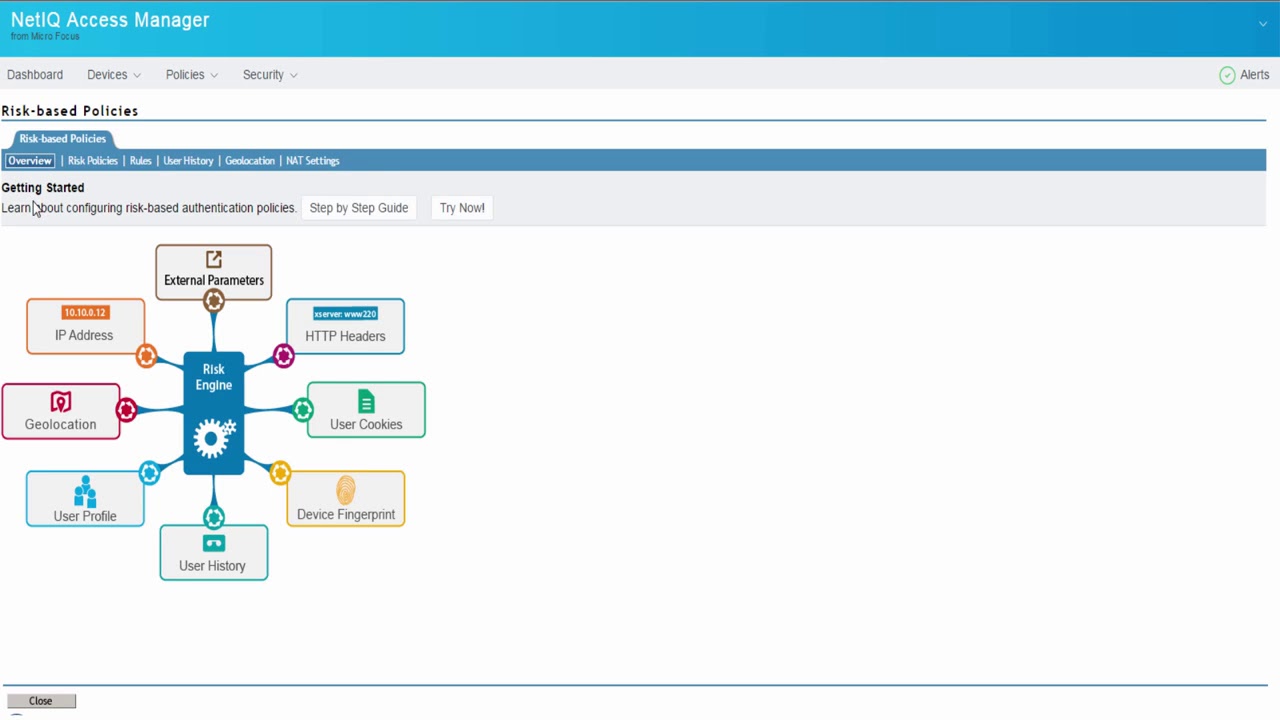
Access Manager Risk Based Authentication Overview

IIS RISK BASED ACCESS CONTROL - LATIKA SHARMA

425 Show | The Importance of Enabling RBCA

3 сертификации, которые сделают вас лучшим специалистом по управлению рисками #кибербезопасность ...

Risk-Based Authentication Policies and Step-Up Authentication

What is Risk Based Security | Centraleyes

What is Risk-based Authentication and what are its benefits?

Journeys with Risk Based Authentication

Sailpoint Risk-based access control | Sailpoint Directory Management